Decentralized biometrics for trust at global scale
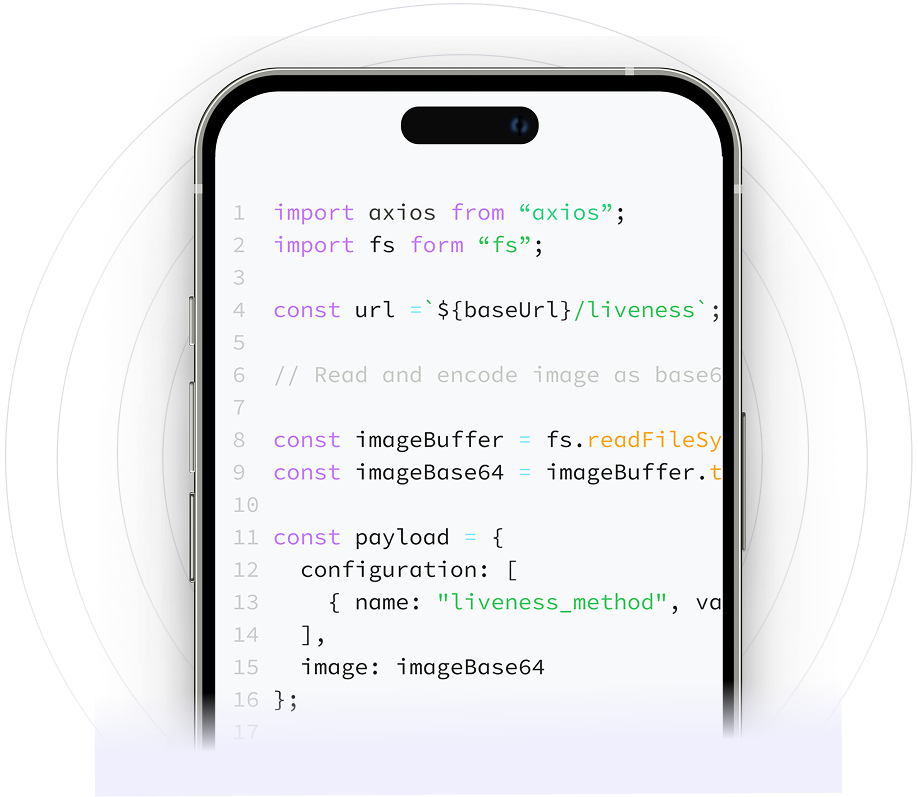
Build custom identity workflows with only 3 lines of code. Faster, more agile and cheaper than legacy identity providers.
Our core identity APIs
Why teams choose Youverse
Reduce fraud, increase conversions and stay compliant with configurable workflows and enterprise controls.
Configurable workflows to fit your business needs.
Significant savings compared to legacy identity providers.
Dedicated support, SLAs and enterprise integrations.
Built to solve real problems across multiple sectors
Fintech & Payments
KYC step-up with liveness
Account takeover prevention
Payment authentication
Gaming & Gambling
Age gates and identity checks
Anti-smurfing/multi-accounting
Fraud and bonus-abuse prevention
Mobility & Retail Apps
Frictionless sign-in and checkout
Age verification
Automated re-verification
Hospitality
Remote check-in
Loyalty app log-in
Facility access
How our decentralized architecture works
1. No Single Point of Attack
Biometric data is split into encrypted shares stored across independent nodes, making breaches mathematically useless.
2. Collusion-Resistant
The protocol prevents collusion, ensuring no combination of nodes can reconstruct or exploit the original biometric template.
3. User-Controlled
Only the user's device can combine distributed proofs to confirm identity, giving users ultimate control over authentication.
4. Business-Governed
Businesses fully govern and audit the verification process making sure the authenticated user is the same that onboarded.
Ready to ship private‑by‑design identity?
Start free in minutes, or connect with our team for custom deployment.
Trusted by businesses like yours
Explore our resources
Don’t miss our latest articles and insights
Stay informed with our latest updates